- Carbon Black Community
- :
- Carbon Black Cloud Release Notes
- :
- Carbon Black Cloud Linux Sensor Release Notes
- :
- Carbon Black Cloud Linux Sensor Release Notes
Carbon Black Cloud Linux Sensor Release Notes
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Carbon Black Cloud Linux Sensor Release Notes
Attention: As of 28 February 2022, Carbon Black Cloud Release Notes are published on VMware Docs. This UEX site will remain but no longer be updated.
2.12
Enterprise EDR hash banning
This feature provides Enterprise EDR customers with the ability to ban process execution by hash.
Background scan
This feature enables a one-time scan of all files on an endpoint. Background scans can be enabled per policy or run on specific endpoints.
VDI improvements
The VDI workflow is enabled with the Linux 2.12 sensor. VDI auto re-registration simplifies the VDI security process for Horizon and Carbon Black Cloud admins.
VDI clones and re-registered devices inherit the policy of the primary image if one exists. Otherwise, clones and re-registered devices are assigned the Virtual Desktop policy or the Standard policy, in that order.
If an organization is using sensor groups, the new device will be moved to the appropriate policy when the metadata matches. See the Sensor Installation Guide for full VDI considerations and see the in-product User Guide for more information about sensor groups.
Installation improvements
This release adds additional installation options to the Linux sensor installer, including:
- Placing the sensor in bypass after installation
- Disabling Live Response
- Only registering the sensor and not starting
- Setting the sensor policy during installation
- Providing proxy server and port parameters to the install script.
Learn more about these new installation options in the Sensor Installation Guide.
Verified sensor upgrade
This release enforces digital signature verification of future sensor upgrades. A sensor kit that cannot be verified will not be accepted as an upgrade by 2.12+ sensors. Sensors 2.11.2 and later are enabled for signature verification.
Distribution support changes
The 2.12 release ends support for the following Linux distribution versions:
- RHEL/CentOS/Oracle 6
- SLES 12 (SP2, SP3)
- OpenSUSE 42.2, 42.3
- Ubuntu 16.04
2.11.3
VMware Carbon Black Cloud Linux sensor version 2.11.3 includes support for installing the sensor on Ubuntu 21 and major improvements/bug fixes.
You can install sensor version 2.11.3 on Ubuntu 21. All sensor features are supported on Ubuntu 21. See the support matrix at Carbon Black Cloud sensor: Linux sensor support.
2.11.2
VMware Carbon Black Cloud Linux sensor version 2.11.2 includes major improvements/bug fixes. We recommend that you upgrade to 2.11.2 on BPF-based systems (4.4+ kernels).
This release supports digital integrity verification of the Linux sensor tar-ball (TGZ) files. Both the RPM and DEB files are digitally signed; this allows customers to verify other file contents within the tar-ball (TGZ).
2.11.1
Carbon Black Cloud Linux sensor version 2.11.1 includes support for specify proxy server details such as Host and Port on the command line while installing the sensor. A new “-p or –proxy” option specifies the proxy server details. See the VMware Carbon Black Cloud Sensor Installation Guide for more information.
2.11.0
Carbon Black Cloud Linux sensor version 2.11.0 includes support for expanded distributions on Endpoint Standard, Debian Support, and other improvements/bug fixes.
Endpoint Standard
Expanded Distribution Support
You can now benefit from uniform coverage across the VMware Carbon Black Cloud platform with expanded distribution coverage. The Linux sensor version 2.11.0 now supports the following distributions:
RHEL 8, CentOS 8, Oracle (RHCK and UEK kernels) 8, Amazon Linux, SUSE, Ubuntu and Debian. See Supported Linux Distributions for more information.
To expand to a wide number of distributions, the Linux sensor is leveraging Extended Berkeley Packet Filters (eBPF or BPF). See the 2.10.1 release for more information.
After the new sensor is installed, Endpoint Standard works as seamlessly as a kernel-based sensor. You can perform the following actions:
- Detect and block known malware
- Add hashes to a custom company banlist
- Add hashes to a custom company allowlist
- Put a sensor into bypass
Endpoint Standard, Enterprise EDR, and Audit & Remediation
Debian Support
Debian is now officially supported on Endpoint Standard, Enterprise EDR, and Audit & Remediation. See Supported Linux Distributions for more information.
2.10.3
VMware Carbon Black Cloud Linux sensor version 2.10.3 includes sensor improvements and bug fixes.
2.10.2
VMware Carbon Black Cloud Linux sensor version 2.10.2 includes sensor improvements and bug fixes.
2.10.1
VMware Carbon Black Cloud Linux sensor version 2.10.1 includes support for expanded distributions on Enterprise EDR, and other improvements/bug fixes.
Enterprise EDR
Expanded distribution support
The Enterprise EDR Linux sensor version 2.10.1 now supports the following distributions:
RHEL 8, CentOS 8, Oracle (RHCK and UEK kernels) 8, Amazon Linux, SUSE, and Ubuntu
See Supported Linux Distributions for more information.
To expand to a wide number of distributions, the Linux sensor is leveraging Extended Berkeley Packet Filters (eBPF or BPF).
BPF provides these key benefits:
- The majority of 4.X and 5.X kernels support BPF by default, which means that expanding to new distributions will be easier (as a compiled kernel module is not required).
- BPF runs safely in a kernel sandbox, so a crash in a BPF program will not crash the kernel.
After the new sensor is installed, Enterprise EDR can be expected to work as seamlessly as a kernel-based sensor. You can perform the following actions:
- Use the Investigate page
- Perform process analysis
- Create watchlists
- Put sensors into bypass
Note: Kernel headers are required for the sensor to function properly. See the Carbon Black Cloud Sensor Installation Guide for additional information.
Audit and Remediation
OSquery update
The Linux sensor version 2.10.1 now supports osquery v4.5.0.
2.9.1
VMware Carbon Black Cloud Linux sensor version 2.9.1 includes RHEL/Oracle 7.9 support and other improvements/bug fixes. This release also ends support for RHEL/CentOS/Oracle 6.5 and below for Audit and Remediation.
RHEL/Oracle 7.9 is now supported on all products. See Supported Linux Distributions.
2.9.0
VMware Carbon Black Cloud Linux sensor version 2.9.0 includes script load event collection on Enterprise EDR, the first version of the open source kernel module, and other improvements/bug fixes. See Supported Linux Distributions.
Enterprise EDR
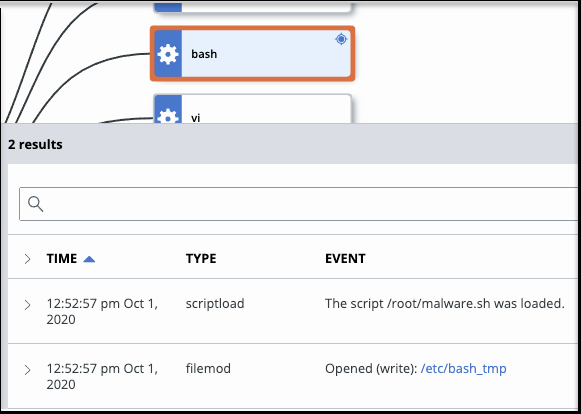
Script load collection
Script files are now reported as a scriptload event of the process that loaded the script. Like all process events on the Process Analysis page, each item is easily searchable and is expandable for more context.
Enterprise EDR and Endpoint Standard
Open Source Linux Kernel
With the release of the 2.9.0 sensor, the kernel module is now open source. Users can contribute and submit bugs through our GitHub page. Link to the Carbon Black Cloud kernel module: https://github.com/vmware/kernel-event-collector-module.
2.8.0
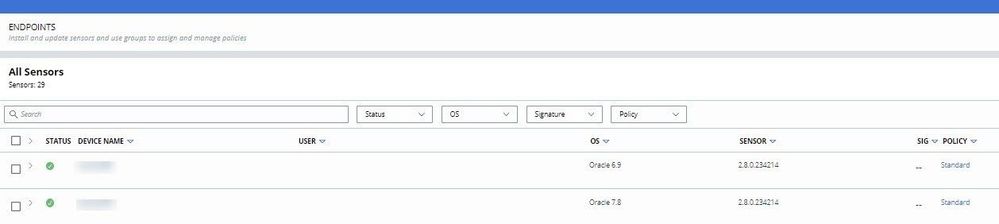
Carbon Black Cloud Linux sensor version 2.8.0 adds Oracle Linux Support to all products on the Carbon Black Cloud platform. It also adds a new event type for file creation events to Endpoint Standard (formerly CB Defense) on RHEL, CentOS and Oracle 6/7, and other improvements/bug fixes. See Supported Linux Distributions.
Endpoint Standard
The Linux sensor supports collection of file creation events for Endpoint Standard.
Note: This feature will be available in prod05 by the end of day 07/01/2020 and 6/30/2020 in all other environments.
All Carbon Black Cloud Products
Oracle Linux Support
- Audit and Remediation (formerly CB LiveOps) is supported on Oracle Linux 6.0-8.2 on both the RHCK kernel and UEK kernel.
- Endpoint Standard (formerly CB Defense) is supported on Oracle Linux 6.6-7.8 on the RHCK kernel.
- Enterprise EDR (formerly CB ThreatHunter) is supported on Oracle Linux 6.6-7.8 on the RHCK kernel.
2.7.1
Carbon Black Cloud Linux sensor version 2.7.1 supports RHEL 7.8 and an update to OpenSSL version 1.1.1g. See Supported Linux Distributions.
RHEL 7.8 is now supported on all products.
2.7.0
Carbon Black Cloud Linux sensor version 2.7.0 supports the first iteration of Endpoint Standard (formerly CB Defense) on RHEL and CentOS 6/7 and other improvements/bug fixes. See Supported Linux Distributions.
VMware Carbon Black Cloud
Sensor diagnostic log collection script
Beginning with the 2.7.0 sensor, the installer now includes a diagnostic log collection script that gathers information. Your support engineer might request that you run the diagnostic log collection script as part of the troubleshooting process.
The diagnostic log collection script collects logs and configuration information from the VMWare Carbon Black Cloud Linux endpoint agent. It also collects various system identity, configuration, and state information. The collected information helps VMware Carbon Black to understand and remediate problems that occur at runtime or during agent installation.
After sensor installation, the script is located here:
/opt/carbonblack/psc/bin/collectdiags.sh
Endpoint Standard (CB Defense) and Enterprise EDR (CB ThreatHunter)
Bypass
The Linux sensor supports the ability to put the sensor into bypass. Bypass mode will turn off event collection and prevention. Live Response will still be functional. Policy level Permission rules (Allow & Log and targeted Bypass rules) are not supported in this version.
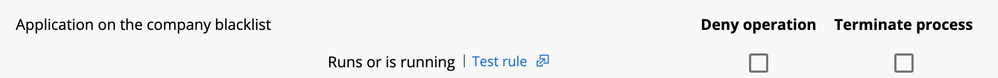
Enterprise Standard
Adding to Company Deny-list
The Linux sensor supports the “runs or is running” policy action when a process reputation is added to the company deny-list.
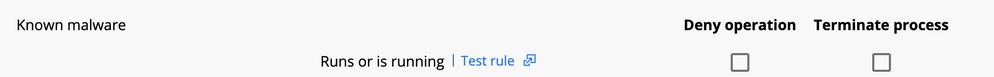
Known Malware
The Linux sensor supports the “runs or is running” policy action when a process reputation is “Known Malware”.
Adding to Company Allow-list
The Linux sensor supports adding hashes to the company allow-list, so you can limit the number of alerts that are triggered from benign processes.
2.6.0
Carbon Black Cloud Linux Sensor version 2.6.0 includes event accuracy improvements and performance improvements for Enterprise EDR. See Supported Linux Distributions.
Enterprise EDR: Add hashes to the company deny-list
- Being opened with execute access
- Starting a process from a file
Processes that have the deny-listed hash loaded at the time that the hash is added to the deny-list are terminated shortly after the sensor receives the updated reputation.
Note: This functionality is enabled in the Linux 2.6.0 GA sensor, but will not be available for use until a future Carbon Black Cloud console release.
Direct User and Command Line installations
Known differences between Linux and other operating systems
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Notification test.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.9.2 release notes have been published.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.10.1 release notes have been published.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.10.2 release notes have been published.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.10.3 release notes have been published.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.11.0 release notes have been published.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.11.1 release notes have been published.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.11.2 release notes have been published.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.11.3 release notes have been published.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Linux sensor 2.12 release notes have been published.
Copyright © 2005-2023 Broadcom. All Rights Reserved. The term “Broadcom” refers to Broadcom Inc. and/or its subsidiaries.