Documentation & Downloads
Browse your product documentation including release notes and installers
The Community will be in read-only mode starting April 19th, 7:00 AM PDT. Check out the blog post!
You will still be able to use the case portal to create and interact with your support cases until the transition, view more information here!
- Carbon Black Community
- :
- Resources
- :
- Documentation & Downloads
- :
- Cb Protection 8.0 Released!
Cb Protection 8.0 Released!
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Cb Protection 8.0 Released!
We are very excited to announce that today we released Cb Protection 8.0 to General Availability.
With this release we reaffirm our commitment to being the preeminent app control product in the market with some very impressive new features.
This release centers around three themes and includes features that you have been clamoring for.
Enterprise Enablement: Providing enterprise-level features enabling greater deployment flexibility across an organization. Features include:
Unified Management: Allows customers to unite multiple Cb Protection servers and manage them from a single console. Capabilities include searching for files, banning and approving files, and pushing software rules to multiple Cb Protection Server instances
Enhanced Role-based Access Controls: Expands on our existing Role-based access controls enabling user permissions to be applied at the policy-level, allowing/disallowing access to specific systems
Application Catalog: Provides insight into what applications and associated versions are installed throughout the environment
Ease of Use: Making the product easier to use is something we continually invest in. For this release, we focused on updating the user interface and improving workflows. Features include:
Enhanced Approval Requests: Improves the workflow to help streamline examining and processing Approval Requests
Design: Delivers a new visual design, including an updated color scheme, layout, navigation, and dynamic scrolling functionality
Everything-at-a-glance Policy Page: Presents the critical information that is applicable to a policy like the computers in that policy and the custom, file, and publisher rules
Prevention & Control: Enhancements in our ability to prevent non-malware based attacks and expanding on our malware based prevention. Features include:
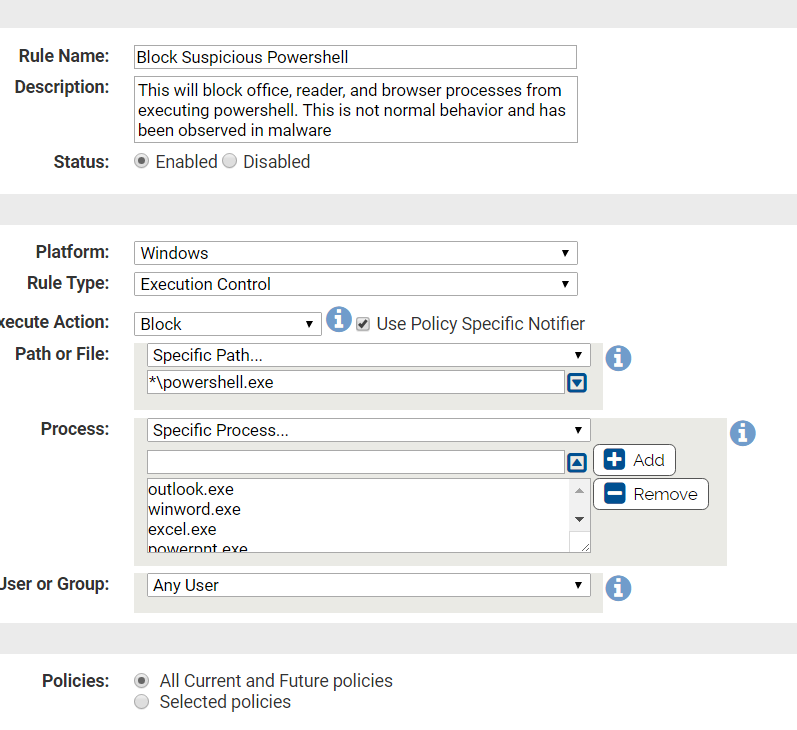
Powershell Exploit Prevention: New rules to look for specific Powershell exploits as well as a new sample rule showing how to look for a common command line attack
Expert Rules: Exposes powerful functionality to our more advanced users, enabling them to do things like tag processes that spawn other processes or files and combine multiple Actions or Operations
Rapid Configs: Delivers configurable, pre-built rule sets that enable easy file approval, application optimization, and OS and application hardening to help customers get faster time-to-value
This release is initially for Windows only. If you have Mac and Linux agents, you can install the 8.0 server and the 7.x Mac and Linux agents will continue to communicate with the Protection server. If you plan to deploy new Mac agents, there is a 7.2.3 Mac agent package with installations instructions available for download. If you intend to install new Linux agents, please reach out to us to get our 7.2.4 Linux agent and become part of our Linux controlled distribution program.
Links to Installer download and documents
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Does this mean we should now be able to write rules in Cb Protection to block certain Powershell attacks that are run from cmd.exe?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
We have a new cmdline macro that allows you to look at the parameters in a command line and then terminate that process. We can't block the process from occurring because we see the parameters once the command line has been called. However, we see the process so quickly that we can terminate it, effectively preventing the process from doing anything.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
That's awesome. I could see where this could also be used to block Powershell that is spawned from Office macros.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Here is a simple rule to block execution of powershell from office documents.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Even easier, Turn on our Microsoft Office Protection Rapid Config which would protect you from powershell and other executables spawning from Office docs.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Lots of info in the docs about Windows 10 Anniversary Update, with Creators Update being released next week where do we stand with support for upgrades with Agent in-place and on-going compatibility? I appreciate that until it is released it is still a little unknown but I'm sure you have a fair idea from the Insider beta releases.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Here's a link that describes our current Creators Update status:
Cb Protection: Windows 10 Creators Update (Redstone 2) Support
Copyright © 2005-2023 Broadcom. All Rights Reserved. The term “Broadcom” refers to Broadcom Inc. and/or its subsidiaries.

