Documentation & Downloads
Browse your product documentation including release notes and installers
The Community will be in read-only mode starting April 19th, 7:00 AM PDT. Check out the blog post!
You will still be able to use the case portal to create and interact with your support cases until the transition, view more information here!
- Carbon Black Community
- :
- Resources
- :
- Documentation & Downloads
- :
- Update to the Carbon Black Defense Local Scanning ...
Update to the Carbon Black Defense Local Scanning Engine
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Update to the Carbon Black Defense Local Scanning Engine
Update 7/17-
In addition to being available via the automated updates, the new signature pack will be available starting tomorrow 7/18 for download from the UI. To download it follow these steps:
- Open endpoints management page by clicking on endpoints on the menu.
- From the sensor options drop down on the top right side choose "download sensor kits".
- When the downloads modal opens, select the latest AV Signature Pack and download.
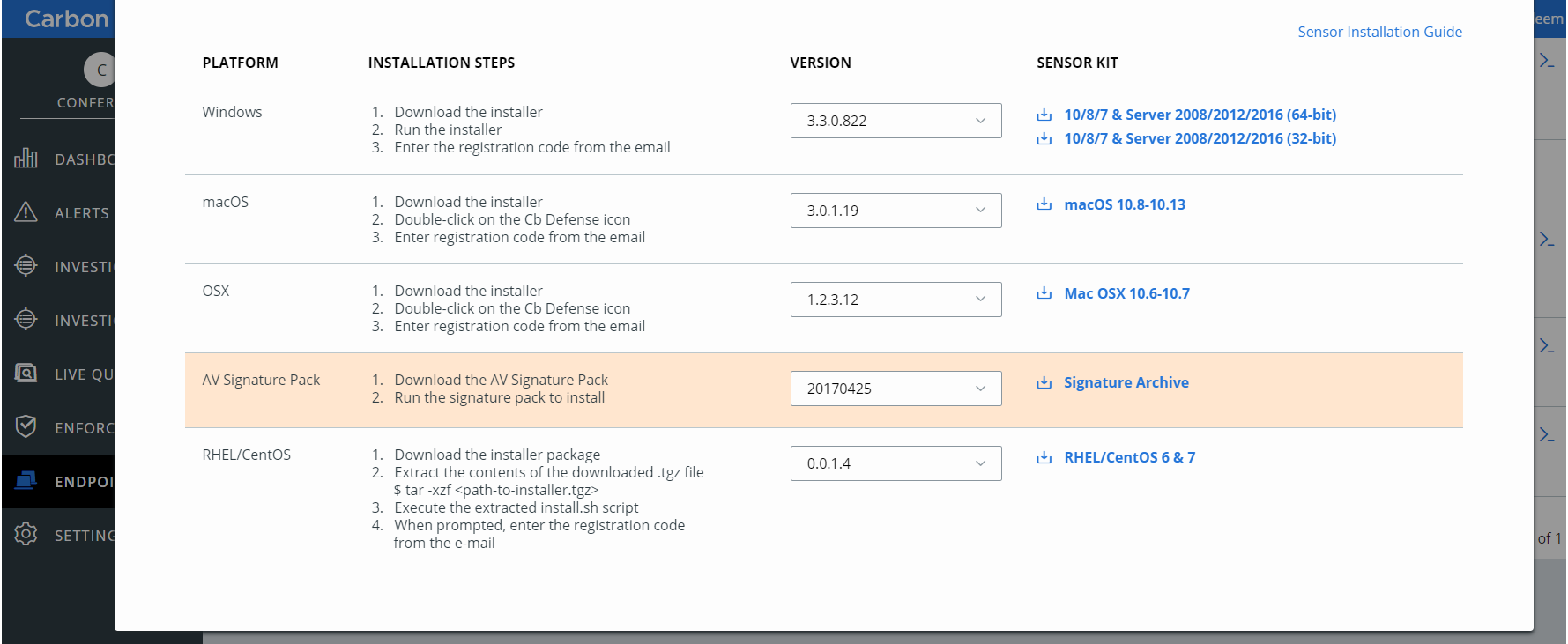
* Note: This is an illustrative screen shot, the version numbers might not reflect latest versions on production environment.
Update 7/16 - The upgrade is now available as scheduled.
Sensors with “Allow Signature Updates” and supported sensor versions will automatically get the upgrade.
The standalone Manual Installer is available at the bottom of this post. The Manual Installer is ONLY available for 3.1 Windows sensors and above. If using the Manual installer, please disable auto-updates in your UI, until Tuesday, July 17th 8 am EST.
Update 7/11 - The upgrade is now scheduled to take place on July 16th. This auto-upgrade will work for all supported sensor versions.
The standalone Manual Installer is now available at the bottom of this post. The Manual Installer is ONLY available for 3.1 Windows sensors and above. If using the Manual installer, please disable auto-updates in your UI, until Tuesday, July 17th 8 am EST.
For clients below 3.1, that have concerns about the automatic upgrade (on July 16th), we recommend setting your Local Scan Settings to update over the largest time window (24 hours). Again, we do not anticipate the auto-upgrade to have any impact on endpoints.
Update: 7/9 - The previous target date for the automatic update of July 10th has been pushed back to July 16th. Carbon Black is working to generate the standalone installer. The automatic installer update will be pushed at a later date, after the standalone installer is generated and distributed via this UeX post. This post will be updated with the standalone installer link as well as more specific timelines in the next few days.
In a few days, Carbon Black will be providing an update to the local scanner deployed to Microsoft Windows Operating Systems that will apply a new technology, that will reduce the size of the signature database by more than 70% percent (without losing any coverage of malicious threats)! This update will result in a reduction of the local file size on the disk (as well as memory usage) and will improve overall scan performance.
This update will first come in the form of a standalone installer so that the rollout can be managed according as your organization sees fit. After the standalone installer is provided, all sensors will undergo an automatic update within a week or two. The exact dates will be provided in a couple of days.
Carbon Black expects this update to be 62 MB in size, and to have a minimal impact.
Although we do not anticipate this update to cause any impact during upgrade, customers with large deployments or reduced network bandwidth may experience temporary network congestion when pulling this update from the cloud.
If there is concern about the amount of traffic that this update will generate on your network, Carbon Black recommends the Manual instructions outlined below:
In order to achieve this performance improvement, please follow the below steps for Automated and Manual download:
Automated
- Ensure “Allow Signature Updates” is enabled on the policy ‘Local Scan’ settings.
- Optional - Increase the window of time between updates to spread the update over a larger period of time. This can be configured from the Local Scan Settings tab within a policy. Options include 2, 4, 8, 12 and 24 hours.
Manual:
- Install a local mirror server to insure that the update is only pulled externally a single time. Please see the following knowledge base document for more information. https://community.carbonblack.com/docs/DOC-5850
- Temporarily disable updates using policy ‘Local Scan’ settings to the local scanner prior to the July 10th delivery date to avoid having the sensors pull the update from the cloud (see image below). Then deploy the update using the provided standalone installer in a controlled manner, then re-enable signature updates via policy settings on July 17th following the update. Please see the following knowledge base document for more information. https://community.carbonblack.com/docs/DOC-5786
Standalone Installer: Installer
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi kyle.donovan,
Do you have any version number or release date information of this AV signature pack?
I still see '20171201' version of signature pack on Prod02 and Prod05 servers, and want to make sure I get the correct version applied.
Also, is there a way check if the intended version of signature pack is applied?
I know that Cb Defense: Verify the Latest Local Scanner Signature Version article can be used for vdf version checks, but is that the correct indicator to check for?
Regards,
Haro
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi haro
We do not have an official version or specific release date for all Production environments at this time. I will be sure to update this post when that information becomes available.
The version number will likely be '20180710' but that is not official yet.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks for the post.
Are there any known issues that this is intended to resolve? Sluggish behavior, etc.? You mention an "improvement in scan performance". Can you elaborate on that one...how does it improve scan performance?
Thanks
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Also, is this update intended to resolve the issue with the 3.2.0.213 version of the CbD sensor not updating the VRF file as described in the article below?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
kyle.donovan - Will all versions of the sensor support this update?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
We have "Allow Signature Updates" disabled, so this will not affect us, correct?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Why would you disable signature updates? Just curious...
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
cbd2020 this update is not intended to resolve that issue, however, we are working on a patch to the 3.2 sensor that should resolve it before this date.
I apologize for the inconvenience.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Because we rolled the agent out in as low impactful way as possible, as we are still explaining ourselves (5 years later) why Cb Protection is so hard on machines. It's not a permanent setting, but we are still in the POC phase, and haven't gotten past the deployment part yet.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Why not bundle this update with the 3.2 fix that your working on, that way, we don't have to go through two different updates.
thanks,
Dan
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Is this still on track for a tomorrow release? We have to disable signature updates and then deploy through our software release process (SCCM). Would like to have updates disabled for as short a time as is possible. Any updates?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
The team is working on the standalone installer now. We hope to provide it within the next couple of days. The automatic rollout is currently scheduled to done about a week or two after the standalone installer is provided. I'll provide additional updates in the coming days regarding timelines.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Question - how much will the CbD sensor download each day with regard to signature updates after this update is released versus what we see today?
I ask because if it's minimal, I may opt to simplify our deployment by pointing all my sensors to the cloud...
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi cbd2020,
You could get rough estimate of the download size by looking at the output from the following command, which to be run from command prompt:
find "size" "C:\Program Files\Confer\scanner\upd.log"
Regards,
Haro
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
You couldn't have chosen a more ominous date? ![]()
Installed - no issues thus far
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi
I have tried the manual update of signature pack available from AV-Sig-Pack-Update-20180711 , and the update seemed to apply correctly.
But right after the update, the vdf files seems to have been rolled back to old version.
Here snippet from related log files:
[scanhost.log]
07:51:15 Versions: Api 4.9.0.264, ave.8.3.52.16:avpack.8.4.3.4:vdf.8.14.61.54:apc.2.10.0.66
09:17:53 Versions: Api 4.9.0.264, ave.8.3.52.16:avpack.8.4.3.4:vdf.8.15.0.174:apc.2.10.0.66
09:31:00 Versions: Api 4.9.0.264, ave.8.3.52.16:avpack.8.4.3.4:vdf.8.14.61.54:apc.2.10.0.66
[upd.log]
09:29:27 Callback: C:\Program Files\Confer\scanner\Data_0\aevdf.dat 8.15.0.174 != 8.14.61.54 -> File will be rolled back
09:29:27 Callback: C:\Program Files\Confer\scanner\Data_0\xbv00000.vdf 7.15.0.32 != 7.14.1.132 -> File will be rolled back
09:29:27 Callback: C:\Program Files\Confer\scanner\Data_0\xbv00001.vdf 8.15.0.146 != 7.14.18.244 -> File will be rolled back
<snip>
09:29:29 Callback: C:\Program Files\Confer\scanner\Data_0\xbv00255.vdf 8.15.0.146 != 8.14.60.146 -> File will be rolled back
Should I have waited until the official release date of July 13th ?
Regards,
Haro
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@haro Did you re-enable auto updates after manual update?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi kyle.donovan,
Oh , I didn't realize I had to turn the auto-updates off.
Sorry for the noise.
Regards,
Haro
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
No problem at all! I always welcome the feedback.
As always, thanks for your help!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
lol...thanks for the update. I did just notice a portal notification that referenced 7/13 for the update so you may want to edit that to reflect 7/16.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Should we be concerned with unexpected reboots of servers? I know the document states there will be no impact, but...
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Carbon Black what is the back out plan?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi mkempers,
In order to control the update, you can disable the auto-update setting on sensors, then follow the steps for manual install on a group of sensors to test it out as noted above, and continue your staggered roll out.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Has anyone experienced issues with the local scanning engine update? I only received one report of a non-responsive endpoint but I suspect it was unrelated.
Question for CB - when we generate a report of our sensors in CSV format from the portal, what do we look at to see if it's running the new engine?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
I see this but am not sure what current engine should be.
| 4.7.0.246-ave.8.3.52.26:avpack.8.4.3.4:vdf.8.15.1.54 |
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
In my talks with the CB personnel that have been working on a few cases with me - VDF: anything 8.15+ indicate new scanning engine update has been picked up.
Moh
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Looks like this does not run silent, is there a switch that can be used to run silently so end users are not inconvenienced?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi jjerome,
From Cb Defense: Best Practices for Deploying Local Scanner , you should be able to use the following.
- To install AV signature pack silently use the following command:
CbDefenseSig-YYYYMMDD.exe /silent
Copyright © 2005-2023 Broadcom. All Rights Reserved. The term “Broadcom” refers to Broadcom Inc. and/or its subsidiaries.

