The Community will be in read-only mode starting April 19th, 7:00 AM PDT. Check out the blog post!
You will still be able to use the case portal to create and interact with your support cases until the transition, view more information here!
- Carbon Black Community
- :
- Carbon Black Threat Advisories
- :
- Threat Advisories Documents
- :
- TAU-TIN - Shade Ransomware
TAU-TIN - Shade Ransomware
- Article History
- Subscribe to RSS Feed
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
TAU-TIN - Shade Ransomware
Threat Analysis Unit - Threat Intelligence Notification
Title: TAU-TIN – Shade Ransomware
Source: https://www.welivesecurity.com/2019/01/28/russia-hit-new-wave-ransomware-spam/
Summary
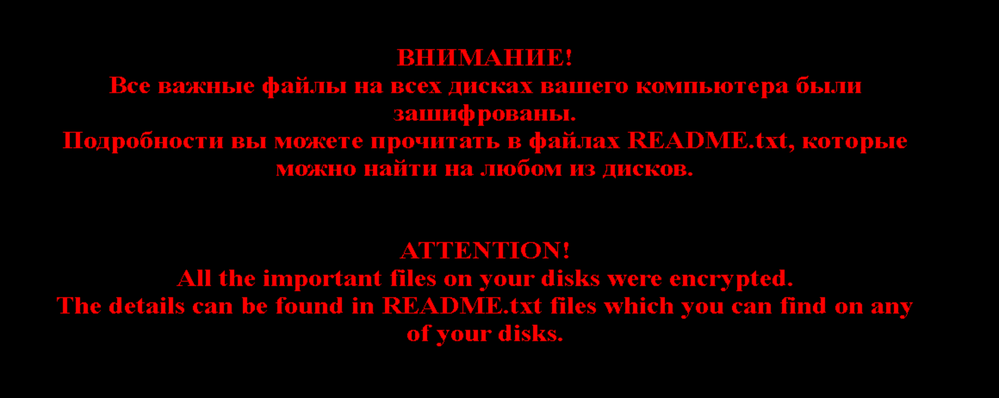
Recently there is a new wave of malicious spam campaign distributing Shade ransomware via sending malicious JavaScript attachments. The spam campaign was mainly targeting users from Russia, and the ransom note was written in both Russian and English. This variant of Shade ransomware will append “.crypted000007” as file extension to the encrypted file. After the encryption is complete, it will change the desktop background as shown in Figure 1.
In addition, it will leave several copies of ransom notes named as “README1.txt”, following until “README10.txt”, the content was shown as in Figure 2.

Shade ransomware will also attempt to delete volume shadow copies to ensure that data cannot be restored easily. Other than that, it will also connect to C&C server, download additional malicious payloads such as crypto-mining malware and install onto the system.
Figure 3: Process tree carried out by the ransomware.
This post serves to inform our customers about detection and protection capabilities within the Carbon Black suite of products against Shade Ransomware.
Copyright © 2005-2023 Broadcom. All Rights Reserved. The term “Broadcom” refers to Broadcom Inc. and/or its subsidiaries.


