Documentation & Downloads
Browse your product documentation including release notes and installers
The Community will be in read-only mode starting April 19th, 7:00 AM PDT. Check out the blog post!
You will still be able to use the case portal to create and interact with your support cases until the transition, view more information here!
- Carbon Black Community
- :
- Resources
- :
- Documentation & Downloads
- :
- PSC Release Notes July 2019
PSC Release Notes July 2019
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
PSC Release Notes July 2019
This July 2019 release notes article contains information about the following releases:
Release calendar
The following table provides a timeline for changes in your CB Predictive Security Cloud (PSC) console. Reference the URL that appears in your browser when you sign into the CB PSC console.
|
Login URL |
ETA |
|
July 29 |
|
|
July 29 |
|
|
July 30 |
|
|
July 31 |
|
|
July 31 |
Predictive Security Cloud
User field now shows Last Active User (macOS)
Based on your feedback, we have updated the User field/column. Previously, the User field/column on the Endpoints, Investigate and Alerts (CB Defense only) pages reflected the username of the account that installed the sensor. The User field/column now shows the last user who was active on the endpoint.
For example, on the Endpoints page, the User column shows the last active user on the endpoint.
This feature requires an upgrade to PSC macOS 3.3.2 sensor and will be available with the upcoming PSC Windows 3.5 sensor. The Linux sensor does not currently support this feature.
This was one of the top requested ideas in our Idea Central and we are pleased to release this feature.
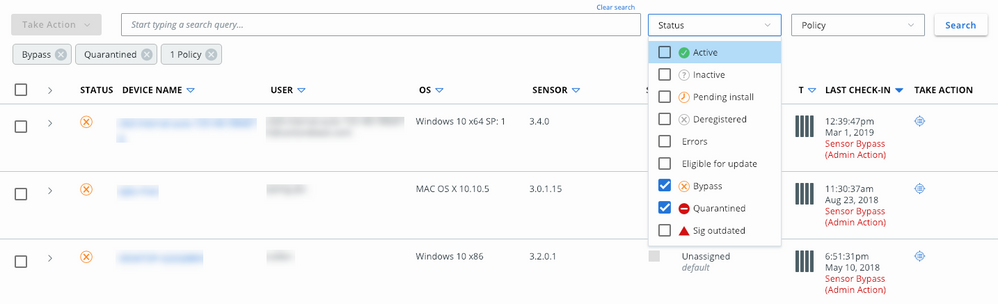
Endpoints page filtering improvements
On the Endpoints page, you can now filter on more than one status and/or policy at a time. This improvement makes it easier to find a particular set of sensors.
Each status filter appears in the header to help clarify the status and policies of the table results.
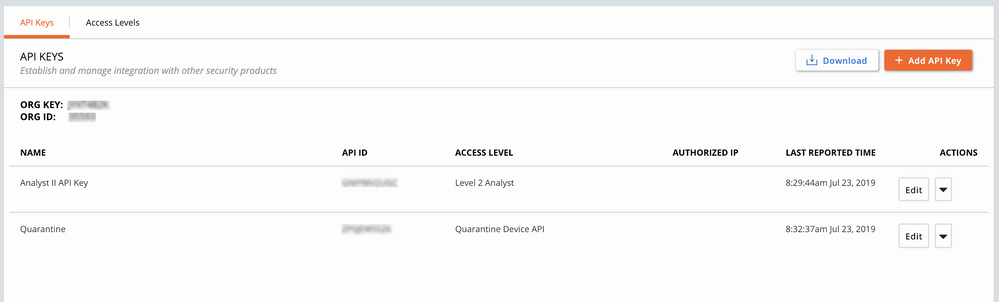
Customizable API access levels
You can now restrict API access in easy and granular ways. All user role access levels, such as “View Only” and “Analyst I”, can be assigned to an API Key. The new Access Levels tab on the API Keys page allows you to create more granular levels of access. See our Developer Relations website.
When you create granular access levels to use with an API Key, you are provided with a list of permissions that are associated with documented, versioned APIs. As we continue to release more documented, versioned APIs, the list of permissions will grow.
Fixed in this release
|
Issue ID |
Description |
|
DSER-10714 |
Incorrect API URLs are no longer displayed in the console. |
|
DSER-15013 |
The Policy Preview window no longer quotes the value that caused wildcards within a query to break. This applies to CB Defense and CB ThreatHunter only. |
Known issues
|
Issue ID |
Description |
|
DSER-4390 |
Devices show only the status of Eligible for Upgrade if the sensor version is lower than any available versions in the Endpoints > Download Sensor Kits window. |
|
DSER-5437 |
Additional HTML can be included in the SIEM event connector. |
|
DSER-10342 |
In some cases, uninstalling a sensor from the console does not trigger an uninstall on the sensor. |
|
DSER-12676 |
An additional alert notification is sent to SIEM or API connectors when an alert is dismissed. |
|
DSER-12728 |
In rare instances, the page renders as a gray screen. |
|
DSER-12858 |
If a backend organization is de-registered, sensors might not be automatically uninstalled. We always recommend that you make note of uninstall codes if they are required. |
|
DSER-15081 |
CB Defense alerts that display in a CB ThreatHunter-enabled organization improperly map script loads as process creation. |
|
DSER-16034 |
Creating a connector with a similar name causes a creation failure. To work around this, make sure that any text before a space is unique for connectors. |
|
DSER-16164 |
The Alerts / Notifications API does not include the ThreatHunter investigate URL; these links do not work. |
|
DSER-16531 |
In rare instances, the sensor does not receive the latest policy information from the backend. |
CB Defense
Detection analytics improvements
Living off the Land Binaries and Scripts (LoLBas) are increasingly popular tools of cyber criminals. These types of attacks leverage native, signed, and pre-installed applications in malicious ways.
We’ve added improved detection of attacks that leverage native Windows applications to perform malicious activity (Living off the Land attacks), as well as attacks that are triggered from a remote machine (a form of lateral movement attack).
We’ve also reduced high-impact false positives that relate to an application that modifies the instructions of another application.
See the following list of improvements for additional details:
|
Type |
Name |
Description |
|
Enhanced Detection |
Rundll32 executing JavaScript |
Improved detection capabilities that are related to Rundll32 executing JavaScript from suspicious HTML applications. |
|
Enhanced Detection |
WinRM leveraged for Lateral Movement |
Improved detection related to attackers using Windows Remote Management (WinRM) to execute suspicious PowerShell commands on behalf of a remote machine. |
|
False Positive |
Instruction setting |
Eliminated False Positive alerts that were related to uncompromised security and communication tools that modified the instructions of Windows processes. |
Fixed in this release
|
Issue ID |
Description |
|
DSER-15748 |
The Reputation filter on the Alerts page did not display any filter options. |
|
DSER-16022 |
When a policy rule is created for Unknown reputation files, these rules are incorrectly applied to NOT_LISTED applications. Because UNKNOWN reputations are very transient, we recommend using and matching both NOT_LISTED and UNKNOWN rules. |
|
DETECT-877 |
In some cases, the Alerts and Alert Triage pages incorrectly showed a block on the primary process (initiator) rather than on the target process. |
Known issues
|
Issue ID |
Description |
|
DSER-9670 |
When searching for Threat Category: Malware on the Alerts page, results can include non-malware results. |
|
DSER-10468 |
If no sensor detail message is entered on a policy, the sensor might display false in the sensor UI. |
|
DSER-10667 |
After whitelisting a file, the reputation on the main Investigate page properly shows WHITE_LISTED although the Application tab incorrectly shows NOT_LISTED. |
|
DSER-11370 |
When dismissing an alert, if a reason is specified, the alert dismissal might fail. |
|
DSER-16223 |
Changes to the auto-blacklist feature are not logged in the audit log. |
|
DSER-16224 |
When a hash is auto-blacklisted, an audit log entry is not added. |
|
DSER-16458 |
When exporting data from the server dashboard, dismissed alerts are not exported when the Include dismissed alerts filter is enabled. |
|
DSER-16508 |
The Tags filter on the Alerts page does not populate with entered tags. |
|
DSER-16563 |
Exporting data from the PSC Dashboard can lead to timeouts when a large amount of data is exported. |
|
DSER-16912 |
The Application Name field on the Investigate page can be blank in situations where multiple names have been sent to the backend by different sensors. |
CB LiveOps
Live Query APIs
To empower you to utilize our products via APIs and to enable deeper integrations with the PSC, we have standardized and publicly documented all CB LiveOps APIs. This exposes all CB LiveOps console functionality, including the following:
- Submit a query
- View query history
- Retrieve query results
- Filter on query results
- View query details
- Retrieve device view results
- Filter on device view results
- Stop a query
- Delete a query
- Export results
To use the CB LiveOps APIs, you must create a Custom API Key that has the correct level of permissions. See our Developer Relations website for additional information about how to access and use these new routes. Queries that run via the API appear in the Query History section of the Live Query page in the console. The User column displays your API token.
Note: Running a large number of complex queries at frequent intervals can negatively impact the endpoints on which they are running. Carefully consider the impact a query will have on endpoints by testing incrementally, especially if you plan to script and schedule queries to run frequently.
CB ThreatHunter
Fixed in this release
|
Issue ID |
Description |
|
TPLAT-6201 |
The First seen as field on the Binary Details page (and from the API) did not return paths in prevalence order; therefore, it was not possible to guarantee the first seen instance. |
|
DSER-13283 |
When you searched for Reports for a new Watchlist, you could not access or add a Report that was returned by the search. |
|
DSER-17222 |
Investigate right pane displayed the same process in the Parent and Process cards on the Processes tab. |
|
DSER-17386 |
Long queries in the Investigate search bar were drawn outside the search bar boundaries. |
Known issues
|
Issue ID |
Description |
|
TPLAT-7568 |
Signatures section of Binary Details page shows unknowns due to signature API endpoint responds with 404 error for binaries that have 1+ digital signatures. |
|
DSER-11445 |
Hovering the mouse on a Investigate search filter hides the percentage values. |
|
DSER-11959 |
When user types - or + and then accepts a suggested search field name, the + or - character is removed from the search bar on the Investigate page. |
|
DSER-12538 |
Binary Details page terminates when UBS APIs return unexpected output. |
|
DSER-13271 |
No field descriptions/examples exist in many suggestions for search fields on the Process Analysis page. |
|
DSER-13295 |
For processes that have a very large number of events, the Process Analysis page for that process can be manually reloaded to load additional events until the query is completed in the background. |
|
DSER-14090 |
If CB Defense is enabled on the PSC with WSC integration enabled, and you remove CB Defense, the WSC integration is not disabled. |
|
DSER-14148 |
When Investigate search bar overflows to multiple lines, you cannot use keyboard navigation or selection. |
|
DSER-14758 |
Searching by device_internal_ip returns no results for CB ThreatHunter-native events on the Investigate page. |
|
DSER-15013 |
Rule Preview links show inconsistent result counts when you use wildcards on the Policies page. |
|
DSER-15052 |
More Watchlist Notification emails are sent than the number of Watchlist hits or alerts. |
|
DSER-15187 |
"process_publisher" searches on the Investigate page lead to signed and unsigned binaries. |
|
DSER-15385 |
Result count drops and rises when changing filters or terms on Investigate search. |
|
DSER-16083 |
When editing a watchlist name or description on the Watchlists page, if the backspace key is used to delete the entire entry, the entry gets rewritten to the original value. This happens if the input is highlighted and deleted or if the backspace key is held. |
|
DSER-16084 |
In the Update Watchlist API, an empty Name field is allowed. |
|
DSER-16087 |
In the Create New Report API, the API responds with a 500 error if a negative timestamp is submitted. |
|
DSER-16190 |
The device_policy field is not always populated in API data or Investigate filters. |
|
DSER-16406 |
Process Count in Rule Preview on Policies page is different from Investigate results count. |
|
DSER-16760 |
Hits popover in Investigate page displays invalid date and no metadata. |
|
DSER-16994 |
After adding a large number of Reports to a Watchlist, the Watchlist will no longer show any Reports in the UI. |
|
DSER-17060 |
event counts on Processes right pane on Investigate page should be shown as "---" not "0" when displaying an enriched result. |
|
DSER-17129 |
Filemods on the Process Analysis page do not display the hash of a file. |
Predictive Security Cloud
Known issues
|
Issue ID |
Description |
|
DSER-16824 |
Searching for “++” with easy search causes an error. |
CB LiveOps
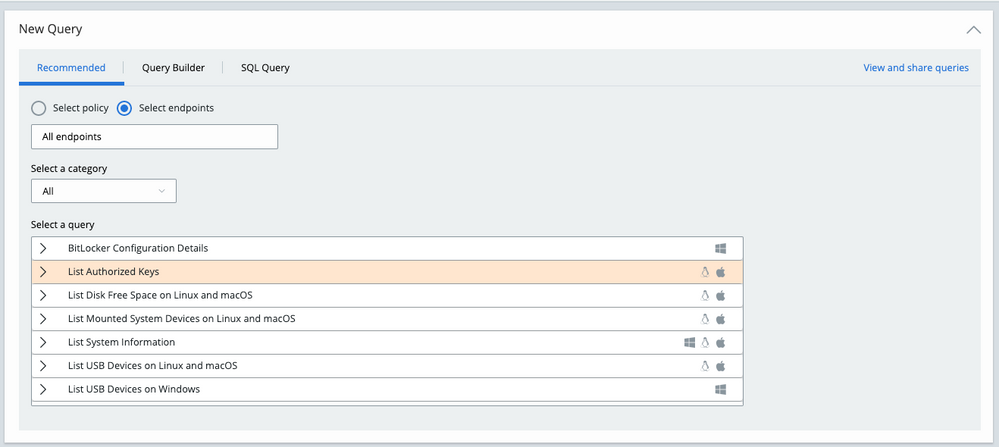
View all recommended queries
To make it easier to browse all expertly crafted Recommended queries in the New Query section, we have changed the filtering logic so that you can see all recommended queries by default without initially choosing a policy or endpoint.
The Recommended query table still filters if you select a policy or endpoint(s) by operating system, or if you select a category.
An error appears if you select an OS-specific query first and then choose a policy or endpoint(s) that the query cannot run on due to OS restrictions; the Run button is disabled. The table then filters based on your policy or endpoint(s) selection.
For example, if you select a Windows-specific query such as BitLocker Configuration Details and then select a Linux endpoint, an error appears and the table shows you Linux-specific recommended queries because the Windows-specific query is not compatible with that endpoint. In this case, you can select a new Linux query, or select an endpoint or policy that works with the query.
The headers on the Recommended tab are now more consistent across tabs, and provide clarity about each section.
Fixed in this release
|
Issue ID |
Description |
|
DSER-15794 |
A misleading error sometimes appeared when selecting multiple endpoints of various operating systems in the New Query section. |
CB ThreatHunter
Search bar layout
The new search bar layout in the Investigate and Alerts pages offers the following improvements:
- More prominent location for the Search Guide link
- More prominent location for the Add search to threat report link
- Changed the button for submitting search from a blue Search button to a white magnifying glass icon
Clear search experience
The "clear search" experience on the search bar in the Investigate, Process Analysis, and Alerts pages has been improved in the following ways:
There is no longer a Clear search link above the search bar. Instead, we have integrated the ability to clear a search with the icon that confirms that your search is using valid syntax. Anytime you have entered any text in the search bar, you can hover your mouse over the icon to the left of your search input. The icon will change to an X, and you can click the X to clear all search input.
Actions menu removal based on user permissions
We removed the Actions menu from Watchlists pages for users who don't have permissions to make changes to Watchlists.
Fixed in this release
|
Issue ID |
Description |
|
DSER-17106 |
Editing IOCs for a custom Threat Report did not succeed for valid changes. |
Known issues
|
Issue ID |
Description |
|
TPLAT-7568 |
Signatures section of the Binary Details page shows unknowns because signature API endpoint responds with a 404 error for binaries that have 1+ digital signatures. |
|
DSER-11445 |
Hovering the mouse on a Investigate search filter hides the percentage values. |
|
DSER-11959 |
When user types - or + and then accepts a suggested search field name, the + or - character is removed from the search bar on the Investigate page. |
|
DSER-12453 |
ThreatHunter Watchlist tags do not show up on the Notes/Tags tab of the Alerts page — these are a different type of tag data. |
|
DSER-12538 |
Binary Details page crashes when UBS APIs return unexpected output. |
|
DSER-13271 |
No field descriptions/examples in many suggestions for search fields on Process Analysis page. |
|
DSER-13283 |
When you search for Reports for a new Watchlist, you cannot access or add a Report that was returned by the search. |
|
DSER-13295 |
For processes that have a very large number of events, the Process Analysis page for that process can be manually reloaded to load additional events until the query is completed in the background. |
|
DSER-13773 |
Watchlist link still shows on the Process Analysis page side panel after the Watchlist is deleted. |
|
DSER-14090 |
If CB Defense is enabled on the PSC with WSC integration enabled, and you remove CB Defense, the WSC integration is not disabled. |
|
DSER-14148 |
When Investigate search bar overflows to multiple lines, you cannot use keyboard navigation or selection. |
|
DSER-14758 |
Searching by device_internal_ip returns no results for CB ThreatHunter-native events on the Investigate page. |
|
DSER-15013 |
Rule Preview links show inconsistent result counts when you use wildcards on the Policies page. |
|
DSER-15052 |
More Watchlist Notification emails are sent than the number of Watchlist hits or alerts. |
|
DSER-15187 |
"process_publisher" searches on the Investigate page lead to signed and unsigned binaries. |
|
DSER-15385 |
Result count drops and rises when changing filters or terms on Investigate search. |
|
DSER-15386 |
When you delete the last Report in an enabled Watchlist, the Reports tab on Watchlists page shows all available reports instead of No Reports for this Watchlist. |
|
DSER-15931 |
Report Search on Watchlists page allows you to submit a search when Search Bar is empty. |
|
DSER-16083 |
On the Watchlists page, the backspace key does not behave as expected to edit a Watchlist name or description. |
|
DSER-16084 |
In the Update Watchlist API, an empty Name field is allowed. |
|
DSER-16087 |
In the Create New Report API, the API responds with a 500 error if a negative timestamp is submitted. |
|
DSER-16190 |
The device_policy field is not always populated in API data or Investigate filters. |
|
DSER-16406 |
Process Count in Rule Preview on Policies page is different from Investigate results count. |
|
DSER-16760 |
Hits popover in Investigate page displays invalid date and no metadata. |
|
DSER-17060 |
Event counts on the Processes pane on the Investigate page should be shown as ---,not 0 when displaying an enriched result. |
|
DSER-17129 |
Filemods on Process Analysis page are not displaying hash of file |
Predictive Security Cloud
Beta roles are generally available
We previously introduced six new beta default roles, making it easier to assign users to have more granular access to PSC features. In mid-July, those new roles officially launch and are no longer in beta status.
Product-specific User Guide content
With this release, product-specific User Guide content for CB Defense and CB ThreatHunter is available through the Help menu on the PSC Console.
CB LiveOps
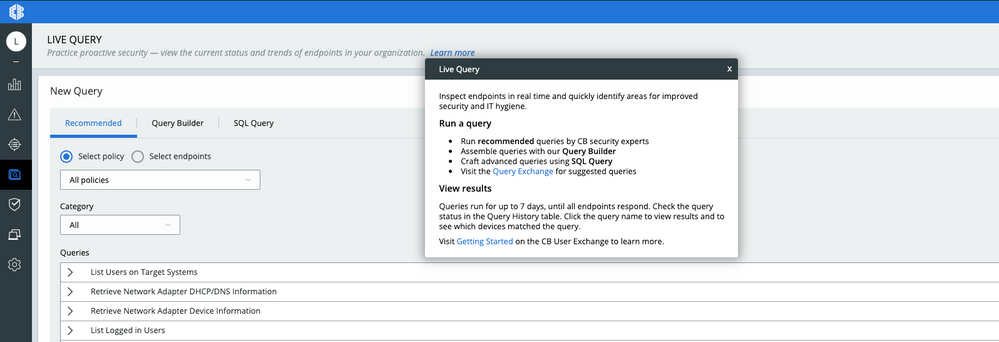
Learn More
A new pop-up window at the top of the Live Query page helps first-time users quickly understand and get value from Live Query. To view this new content, click the Learn More link in the header of the Live Query page.
Previously, the Learn More link opened the Live Query Getting Started Guide on the User Exchange; this is now an embedded link in the Learn More window that provides the information directly from the PSC console.
Fixed in this release
|
Issue ID |
Description |
|
DSER-16968 |
Complex queries (for example, with UNION) sometimes caused the Results page to show an error. |
CB ThreatHunter
Additional context on the Investigate page
The PSC now provides additional process context on the same page as the search results. You can select a result and view related devices, users, policies, and reputation, as well as all available PSC remediation actions. This makes it easy to spot potentially malicious anomalies and take swift action in just a few clicks.
Example:
Example of a fully expanded PROCESS panel:
Example of the available actions on the Actions menu:
Also in this release
When searching on the Investigate page, the suggested field names include only the fields that are relevant to the PSC products that your organization uses.
For example, the ttp field is only suggested when you are running both CB Defense and CB ThreatHunter. The process_name field is suggested for CB Threathunter and CB Defense or CB ThreatHunter-only customers. It is not suggested for CB Defense-only customers.
Fixed in this release
|
Issue ID |
Description |
|
DSER-13177 |
Fixed issue where User Guide option was not available through the Help menu in the PSC Console. |
Known issues
|
Issue ID |
Description |
|
TPLAT-6201 |
The First seen as field on the Binary Details page (and from the API) does not return paths in prevalence order; therefore, it is not possible to guarantee the actual first seen instance. |
|
DSER-11445 |
Hovering the mouse on a Investigate search filter hides the percentage values. |
|
DSER-11959 |
When user types - or + and then accepts a suggested search field name, the + or - character is removed from the search bar on the Investigate page. |
|
DSER-12453 |
ThreatHunter Watchlist tags do not show up on the Notes/Tags tab of the Alerts page — these are a different type of tag data. |
|
DSER-12538 |
Binary Details page crashes when UBS APIs return unexpected output. |
|
DSER-13271 |
No field descriptions/examples exist in many suggestions for search fields on Process Analysis page. |
|
DSER-13283 |
When you search for Reports for a new Watchlist, you cannot access or add a Report that was returned by the search. |
|
DSER-13295 |
For processes that have a very large number of events, the Process Analysis page for that process can be manually reloaded to load additional events until the query is completed in the background. |
|
DSER-13773 |
The Watchlist link still shows on the Process Analysis page side panel after the Watchlist is deleted. |
|
DSER-14090 |
If CB Defense is enabled on the PSC with WSC integration enabled and you remove CB Defense, the WSC integration is not disabled. |
|
DSER-14148 |
When Investigate search bar overflows to multiple lines, you cannot use keyboard navigation or selection. |
|
DSER-14758 |
Searching by device_internal_ip returns no results for CB ThreatHunter-native events on the Investigate page. |
|
DSER-15013 |
Rule Preview links show inconsistent result counts when you use wildcards on the Policies page. |
|
DSER-15052 |
More Watchlist Notification emails are sent than the number of Watchlist hits or alerts. |
|
DSER-15187 |
process_publisher searches on the Investigate page lead to signed and unsigned binaries. |
|
DSER-15385 |
Result count drops and rises when changing filters or terms on Investigate search. |
|
DSER-15386 |
When you delete the last Report in an enabled Watchlist, the Reports tab on the Watchlists page shows all available reports instead of No Reports for this Watchlist. |
|
DSER-15931 |
Report Search on the Watchlists page lets you submit a search when the Search Bar is empty. |
|
DSER-16083 |
On the Watchlists page, the backspace key does not behave as expected to edit a Watchlist name or description. |
|
DSER-16084 |
In the Update Watchlist API, an empty Name field is allowed. |
|
DSER-16087 |
In the Create New Report API, the API responds with a 500 error if a negative timestamp is submitted. |
|
DSER-16190 |
The device_policy field is not always populated in API data or Investigate filters. |
|
DSER-16406 |
Process Count in Rule Preview on Policies page is different from Investigate results count. |
|
DSER-16760 |
Hits popover in the Investigate page displays invalid date and no metadata. |
Carbon Black, Inc. | 1100 Winter Street, Waltham, MA 02451 ?USA | Tel: 617.393.7400
Copyright © 2011–2019 Carbon Black, Inc. All rights reserved. Carbon Black, CB Defense, Cb ThreatHunter, CB ThreatSight, and CB LiveOps are registered trademarks and/or trademarks of Carbon Black, Inc. in the United States and other countries. All other trademarks and product names may be the trademarks of their respective owners.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks! Wow!
FYI, clicking "Sig Outdated" clears all other filters within the Endpoints section
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@cstamand Good catch, just checked and this is a known bug. Keep the feedback coming!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Also, selecting any of the filters and selecting "clear search" doesn't clear the filters. Is this by design?
I think it'd be much better design wise to have a "X" at the very end of the right to clear the search field, and a "reset search" button for everything including filters.
Copyright © 2005-2023 Broadcom. All Rights Reserved. The term “Broadcom” refers to Broadcom Inc. and/or its subsidiaries.